A detailed survey of denial of service for IoT and multimedia systems: Past, present and futuristic development | SpringerLink
Internet of Things Applications, Security Challenges, Attacks, Intrusion Detection, and Future Visions: A Systematic Review
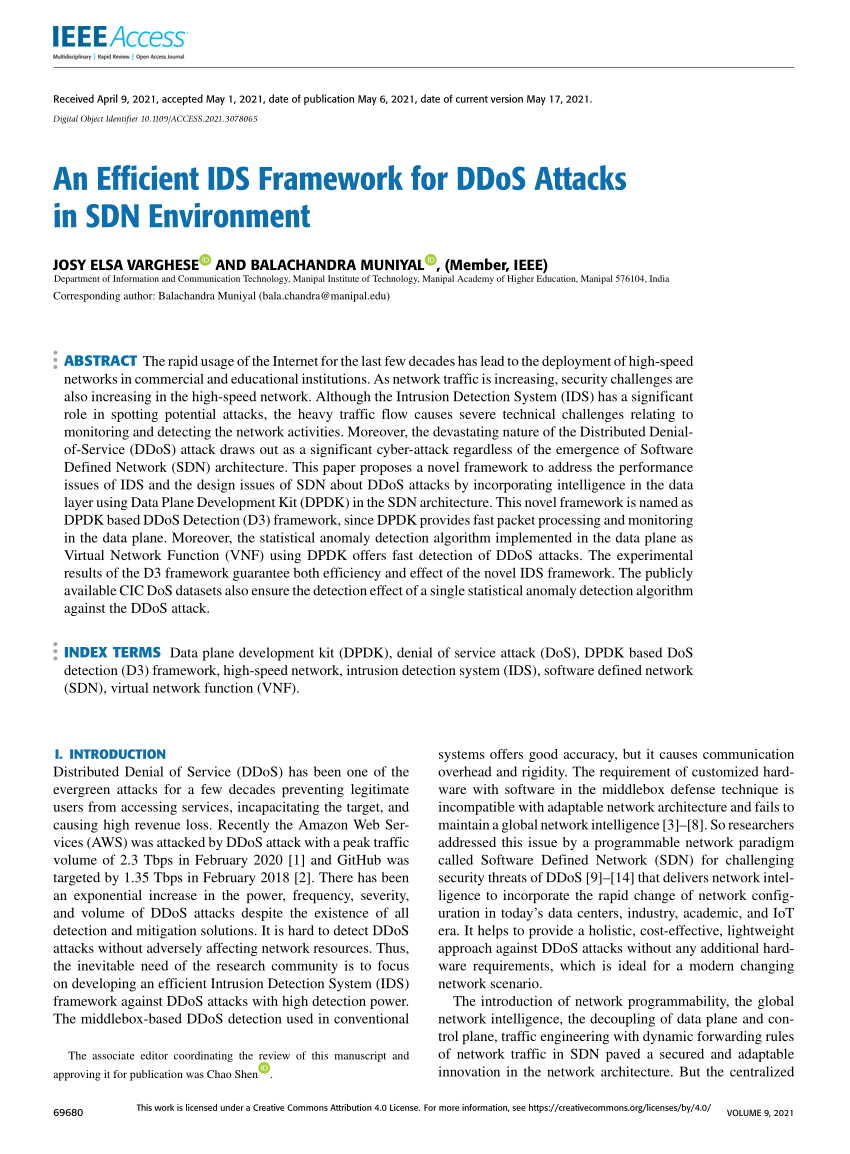
Machine Learning Based Approach for Detecting Distributed Denial of Service Attack by Qozeem Adeniyi Adeshina A project report s
Machine Learning Based Approach for Detecting Distributed Denial of Service Attack by Qozeem Adeniyi Adeshina A project report s
Machine Learning Based Approach for Detecting Distributed Denial of Service Attack by Qozeem Adeniyi Adeshina A project report s
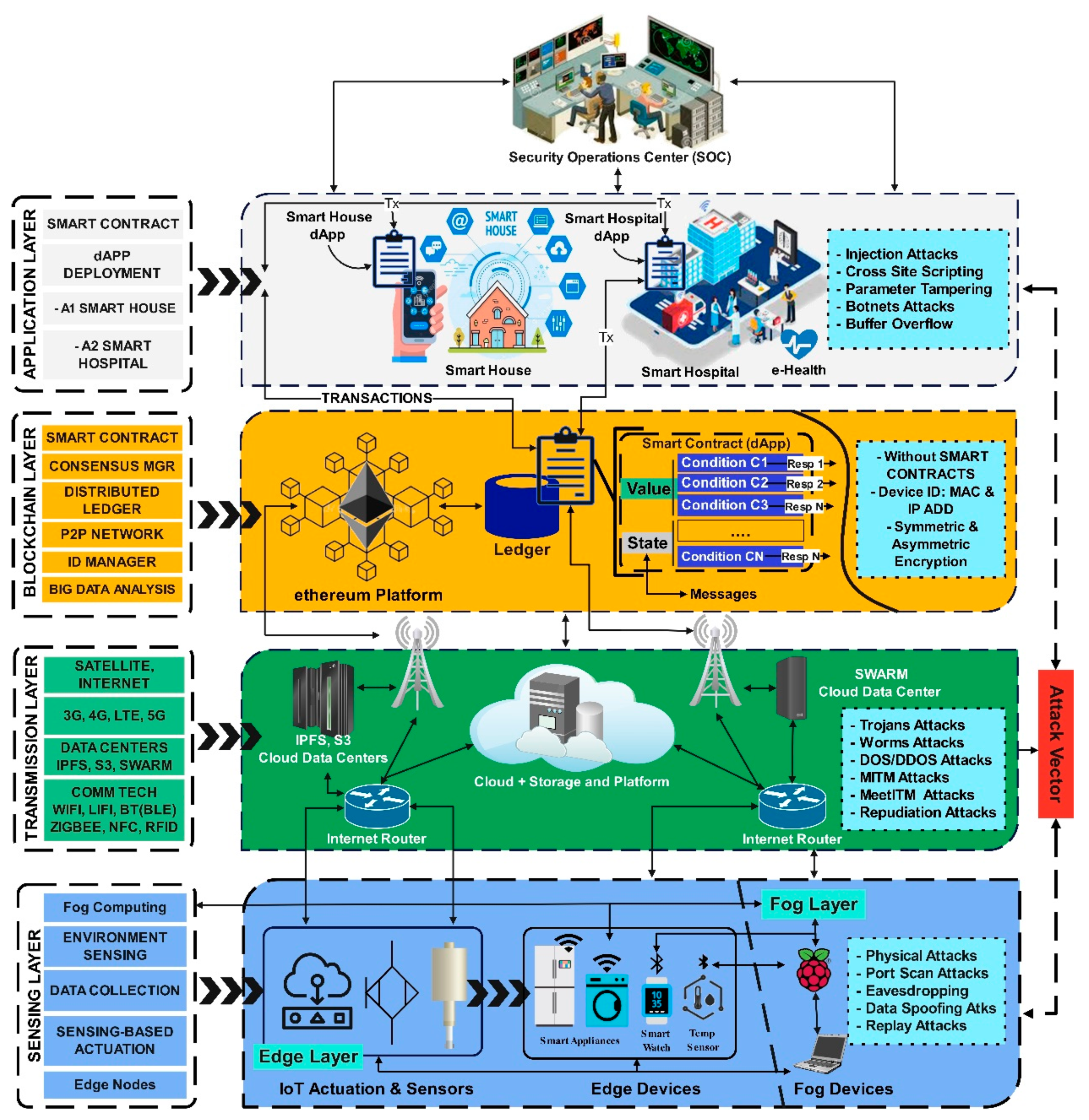
Sensors | Free Full-Text | A Comparative Analysis on Blockchain versus Centralized Authentication Architectures for IoT-Enabled Smart Devices in Smart Cities: A Comprehensive Review, Recent Advances, and Future Research Directions